The Hidden Risk of “It’s Been Working for Years”
There’s a phrase heard in network teams everywhere:
“It’s been working for years.”
It sounds reassuring. It sounds stable. It sounds safe.
But in modern enterprise environments, it can be one of the most dangerous assumptions in IT.
Stability Is Not the Same as Security
A configuration that hasn’t changed in five years is not necessarily secure.
In fact, it may be:
- Running outdated encryption standards
- Allowing legacy management protocols
- Missing modern hardening requirements
- Violating new compliance frameworks
- One undocumented change away from an outage
The network doesn’t fail loudly when risk accumulates. It fails when a trigger event exposes it.
Configuration Drift Happens Quietly
Over time:
- Emergency changes are made and never rolled back
- Temporary access is left permanently enabled
- SNMP communities remain configured long after migration to SNMPv3
- Test ACL entries remain in production
- Password standards evolve — but configs do not
This is called configuration drift — and it happens in every environment.
Without automated validation, drift becomes invisible.
Compliance Requirements Change — Even If Your Config Doesn’t
PCI, SOX, HIPAA, internal security policies — they evolve.
A configuration that passed audit in 2021 may fail in 2026.
Security expectations shift:
- Telnet once acceptable → now prohibited
- SNMPv2 once common → now high risk
- Weak ciphers once allowed → now blocked
If your validation process is manual, you are always behind.
The Real Risk: Undetected Change
Most major outages and breaches are not caused by brand-new deployments.
They’re caused by:
- A small change made months ago
- A misconfigured ACL
- A removed logging statement
- A firmware upgrade that altered behavior
- A credential policy change not applied consistently
The issue isn’t that the network “stopped working.”
It’s that no one noticed it slowly becoming vulnerable.
Manual Audits Don’t Scale
In large environments:
- Hundreds or thousands of devices
- Multiple OS versions
- Hybrid cloud connectivity
- Remote offices and distributed edge
Manual CLI spot-checks cannot provide continuous assurance.
Spreadsheets cannot serve as a source of truth.
And tribal knowledge disappears when engineers move on.
Proactive vs Reactive Network Management
The shift modern IT teams are making:
| Reactive Model | Proactive Model |
|---|---|
| Fix after outage | Detect drift automatically |
| Manual spot checks | Continuous compliance validation |
| Engineer memory | Policy-driven enforcement |
| “It’s been working” | “It’s continuously verified” |
The difference is not tooling alone. It’s mindset.
What Modern Teams Do Differently
Forward-looking network teams:
- Automatically back up configurations nightly
- Compare running configs against policy baselines
- Alert on unauthorized changes
- Enforce encryption and access standards
- Generate audit-ready compliance reports
They do not assume stability.
They verify it — continuously.
The Strategic Shift
In today’s environment — where networks underpin AI initiatives, cloud adoption, remote work, and zero-trust security — the cost of hidden risk is higher than ever.
“It’s been working for years” is no longer a comfort.
It’s a warning sign.
Move from Assumption to Assurance
If your network hasn’t been continuously validated against policy, you don’t have stability.
You have accumulated risk.
Ready to See What’s Drifted?
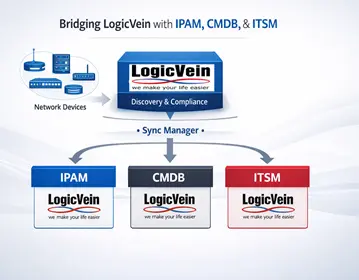
Modern network configuration management platforms like LogicVein Net LineDancer provide:
- Automated configuration backups
- Drift detection
- Policy-based compliance validation
- Multi-device comparison
- Audit-ready reporting
Stop assuming. Start verifying.
👉 Learn how LogicVein helps enterprise IT and MSP teams eliminate hidden configuration risk.
Ready to See More?
Whichever approach fits your environment, LogicVein supports it. Watch our series of videos here or see all our features here to see how LogicVein can simplify your network operations while keeping access tightly controlled. Ready to see LogicVein in action? Request a Demo and discover how you can simplify operations, improve reliability, and gain full network visibility.
#LogicVein #SmartBridge #NetworkAutomation #NetworkManagement #NetworkCompliance #ChangeManagement #MSPTools #MultiVendorNetworks #NCCM