How Modern Network Teams Escape the Reactive Trap
🔥 The Firefighting Trap
If you’ve worked in network operations long enough, you know the cycle:
- Interface down at 2:13 AM
- SNMP alert storm
- SSH into the device
- Grab the running-config
- Compare with “last known good”
- Patch the issue
- Hope it doesn’t happen again
Rinse. Repeat.
Many Enterprise IT and MSP teams operate in a constant reactive state — responding to outages, scrambling during change windows, and manually investigating configuration drift.
Firefighting consumes time that should be invested in prevention.
🚨 Why Reactive Network Management Fails
Reactive operations create:
- Slow incident resolution
- Inconsistent configuration standards
- Compliance risk exposure
- Change management chaos
- Burned-out engineers
When visibility depends on logging into devices individually, you’re already behind.
🔄 The Shift: From Reactive to Proactive
Modern network management flips the model:
| Reactive | → | Proactive |
|---|---|---|
| Manual config backups | → | Automated nightly backups |
| After-the-fact audits | → | Continuous compliance validation |
| SSH troubleshooting | → | Centralized visibility |
| Spreadsheet tracking | → | Policy-driven automation |
| Panic rollback | → | One-click restore |
The goal isn’t faster firefighting.
It’s eliminating the fire.
🧠 What Proactive Network Management Looks Like
1️⃣ Continuous Configuration Monitoring
Automatically archive configurations and detect drift.
Move from:
“What changed?”
to
“Why was this changed — and was it authorized?”
2️⃣ Compliance Built Into Operations
Validate device configurations against internal policies or regulatory frameworks.
Be audit-ready at any time — not just before an audit.
3️⃣ Controlled, Auditable Changes
- Capture pre-change snapshots
- Execute standardized change workflows
- Validate post-change results
- Maintain immediate rollback capability
No more blind changes.
4️⃣ Secure Remote Access & Visibility
- Centralized SSH access
- Session logging
- Role-based access control
- Zero-trust enforcement
Security becomes part of operations — not an afterthought.
📊 The Operational Maturity Model
- Ad Hoc – Manual configs, tribal knowledge
- Reactive – Monitoring exists, but no automation
- Structured – Backups + basic compliance
- Automated – Policy enforcement + drift detection
- Optimized – Self-correcting workflows + zero-trust access
Most organizations believe they are at Level 3.
Few are truly past Level 2.
📈 Real-World Impact
Organizations that transition from firefighting to proactive management report:
- Significant reduction in configuration-related incidents
- Faster MTTR
- Fewer emergency change windows
- Improved audit posture
- Reduced operational stress
Engineers shift from reactive troubleshooting to strategic initiatives.
🏗️ What Makes the Transition Possible?
- Centralized configuration intelligence
- Policy-driven enforcement
- Role-based access control
- Automated backup & restore
- Event-driven workflows
Firefighting disappears when the network becomes predictable.
🎯 The Strategic Advantage
When your network is:
- Version-controlled
- Continuously monitored
- Compliance-validated
- Securely accessed
- Automated for common tasks
You stop reacting to problems.
You start engineering resilience.
That’s the difference between:
“Keeping the lights on”
and
Building the future.
🚀 Ready to Move Beyond Firefighting?
If your team is spending more time reacting than planning, it may be time to evolve.
Modern network automation platforms enable Enterprise IT and MSP teams to:
- Automate backups
- Enforce compliance
- Control change workflows
- Secure remote access
- Eliminate configuration drift
Predictable networks don’t happen by accident.
They’re engineered.
Ready to See More?
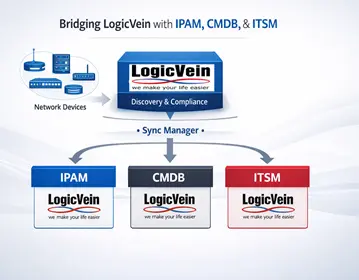
Whichever approach fits your environment, LogicVein supports it. Watch our series of videos here or see all our features here to see how LogicVein can simplify your network operations while keeping access tightly controlled. Ready to see LogicVein in action? Request a Demo and discover how you can simplify operations, improve reliability, and gain full network visibility.
#LogicVein #SmartBridge #NetworkAutomation #NetworkManagement #NetworkCompliance #ChangeManagement #MSPTools #MultiVendorNetworks #NCCM